AutoPhish vs Threat Watch
Side-by-side comparison to help you choose the right tool.
AutoPhish enhances security awareness through AI-driven phishing simulations and tailored training for your team.
Last updated: March 1, 2026
Threat Watch
Assess your cybersecurity health instantly and gain insights to strengthen defenses against emerging threats.
Last updated: March 1, 2026
Visual Comparison
AutoPhish

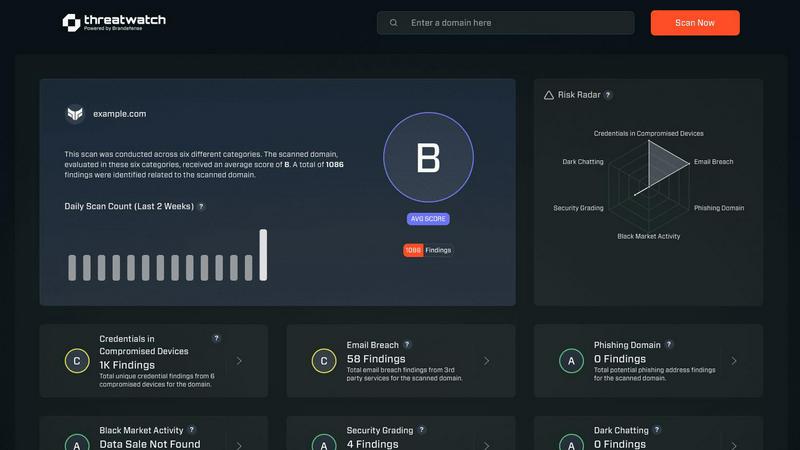
Threat Watch
Feature Comparison
AutoPhish
Realistic AI Simulations
AutoPhish harnesses the power of AI to create phishing emails that closely mimic real-world attacks, ensuring that simulations are relevant and industry-specific. This realism allows organizations to effectively prepare their employees for potential threats.
Automated Campaigns
The platform allows users to schedule and run phishing tests automatically, saving valuable time and ensuring consistent training for all employees. This automation streamlines the process, making it easier to maintain an ongoing security awareness program.
Targeted Training
Based on the results of phishing simulations, AutoPhish offers targeted security awareness training tailored to specific user roles. This personalized approach enhances the learning experience and effectively addresses individual vulnerabilities within the organization.
Comprehensive Reporting
AutoPhish provides advanced reporting features that allow organizations to monitor simulation results, identify vulnerable users, and track progress over time. These insights are crucial for continuous improvement and strategic planning in cybersecurity efforts.
Threat Watch
Real-Time Insights
Threat Watch offers real-time insights into your organization's cybersecurity landscape, allowing for immediate detection of vulnerabilities and threats. This feature ensures that users are always aware of their security posture and can act quickly to address issues as they arise.
Automated Assessments
With automated assessments, Threat Watch streamlines the process of evaluating security risks. Organizations can benefit from comprehensive evaluations without the need for extensive manual reviews, saving time and resources while enhancing security measures.
Dark Web Monitoring
One of the standout features of Threat Watch is its dark web monitoring capability. This feature scans the dark web for compromised credentials and sensitive information, providing users with critical alerts that enable them to take swift action to protect their digital identity.
Comprehensive Security Evaluations
Threat Watch evaluates multiple critical security categories, including compromised devices, breached accounts, and phishing addresses. This comprehensive approach ensures that organizations have a complete understanding of their security vulnerabilities and can prioritize their mitigation efforts effectively.
Use Cases
AutoPhish
Employee Awareness Enhancement
Organizations can use AutoPhish to increase employee awareness regarding phishing attacks, enabling staff to identify and respond to threats effectively. This proactive training leads to a more security-conscious workforce.
Vulnerability Assessment
IT security teams can leverage AutoPhish to identify specific vulnerabilities within their teams through realistic simulations. This insight allows for targeted interventions before actual threats can exploit these weaknesses.
Compliance and Reporting
Compliance officers can utilize AutoPhish to ensure adherence to industry regulations and standards by demonstrating ongoing training efforts and vulnerability assessments through detailed reporting features.
Incident Response Preparation
AutoPhish equips organizations with the tools needed to prepare for potential security incidents. By familiarizing employees with real-world phishing scenarios, the platform enhances overall incident response capabilities.
Threat Watch
Small Business Cybersecurity
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch enables these organizations to quickly identify vulnerabilities, ensuring they can protect their assets without requiring a large security team.
Enterprise Risk Management
Large enterprises face complex cybersecurity challenges. Threat Watch provides a centralized solution for identifying and managing risks across diverse departments, making it easier to implement comprehensive security strategies.
Incident Response Preparation
Organizations can use Threat Watch for proactive incident response preparation. By regularly assessing their cybersecurity health, companies can develop and refine their incident response plans, ensuring they are ready to act swiftly in the event of a breach.
Compliance and Regulatory Needs
Many industries have strict compliance requirements regarding data security. Threat Watch helps organizations meet these regulations by providing detailed assessments and reports that demonstrate their commitment to cybersecurity best practices.
Overview
About AutoPhish
AutoPhish represents a transformative leap in proactive cybersecurity defense, enabling organizations to shift from a reactive stance to a culture of continuous, intelligent vigilance. This AI-powered platform is meticulously crafted to strengthen the human element of your security—your employees—by offering hyper-realistic phishing simulations and tailored, role-based security awareness training. It is specifically designed for IT security teams, compliance officers, and business leaders across organizations of all sizes that recognize social engineering as the primary attack vector in today's threat landscape. The core value proposition of AutoPhish lies in its capacity to intelligently replicate real-world attacker behaviors at scale, identifying specific vulnerabilities within your workforce before they can be exploited by malicious actors. By automating the entire cycle of testing, analysis, and education, AutoPhish transforms security awareness from a mere compliance checkbox into a dynamic, integral component of operational resilience. This progressive approach ensures that your team's defensive capabilities evolve in tandem with the ever-changing threat landscape, fostering a genuinely security-aware culture capable of withstanding and adapting to emerging phishing tactics.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution that empowers organizations to confront and conquer the ever-evolving landscape of cyber threats. By meticulously assessing assets, vulnerabilities, and exposures, Threat Watch delivers a holistic view of an organization's cybersecurity health. This tool is designed for a diverse range of businesses, from nimble startups to expansive enterprises, enabling them to swiftly identify critical security gaps. The primary value proposition of Threat Watch lies in its capability to provide real-time insights and automated assessments, equipping users with the tools to identify, prioritize, and mitigate risks effectively. As cyber threats become increasingly sophisticated, Threat Watch evolves alongside them, ensuring users are always equipped to protect their digital assets and sensitive information. With Threat Watch, organizations not only bolster their security posture but also cultivate a proactive culture of risk management, fostering resilience in the face of potential cyber adversities.
Frequently Asked Questions
AutoPhish FAQ
What is AutoPhish?
AutoPhish is an AI-powered platform that provides organizations with realistic phishing simulations and targeted security awareness training to bolster their cybersecurity posture and create a culture of vigilance.
How does AutoPhish create realistic simulations?
The platform uses advanced AI algorithms to craft phishing emails that closely mimic real-world attacks, ensuring that simulations are relevant and tailored to the specific threats faced by different industries.
Can I automate my phishing testing campaigns?
Yes, AutoPhish allows users to automate phishing testing campaigns, making it easy to schedule and run simulations without the need for constant manual intervention, thereby ensuring consistent training.
How does AutoPhish help with compliance?
AutoPhish assists organizations in meeting compliance requirements by providing detailed reporting on user performance during phishing simulations, demonstrating ongoing training efforts, and identifying areas for improvement.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes, from startups to large enterprises. Its adaptable features make it suitable for any business looking to enhance its cybersecurity measures.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms to scan the dark web for compromised credentials and sensitive information related to your organization. This proactive monitoring allows users to receive timely alerts about potential threats.
Is Threat Watch easy to integrate with existing systems?
Yes, Threat Watch is designed with ease of integration in mind. It can seamlessly connect with existing security infrastructure, enabling organizations to enhance their cybersecurity posture without disrupting their current operations.
Can Threat Watch help with compliance reporting?
Absolutely. Threat Watch provides detailed assessments and reports that can assist organizations in meeting compliance requirements related to cybersecurity, helping them demonstrate their commitment to data protection and risk management.
Alternatives
AutoPhish Alternatives
AutoPhish is an innovative platform that belongs to the category of cybersecurity and security awareness training. It utilizes advanced AI technology to deliver hyper-realistic phishing simulations and targeted training, designed to enhance the human element of security within organizations. Users often seek alternatives to AutoPhish due to various reasons, including budget constraints, specific feature requirements, or the need for compatibility with existing platforms. When exploring alternatives, it’s essential to consider factors such as the comprehensiveness of phishing simulations, the level of automation offered, and the adaptability of the training materials to your organization's unique context. A solution that prioritizes continuous learning and aligns with your security objectives will foster a more resilient security culture.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution that empowers organizations to assess their cybersecurity health and take actionable steps against emerging threats. Belonging to the business intelligence category, it meticulously analyzes assets, vulnerabilities, and exposures to provide a comprehensive overview of an organization’s cyber landscape. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms. When selecting an alternative, it is crucial to consider factors such as real-time threat intelligence, automated assessments, and the ability to monitor dark web activity. Ensuring that the solution aligns with your organization’s unique cybersecurity needs will facilitate a more effective defense strategy.

