Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right tool.
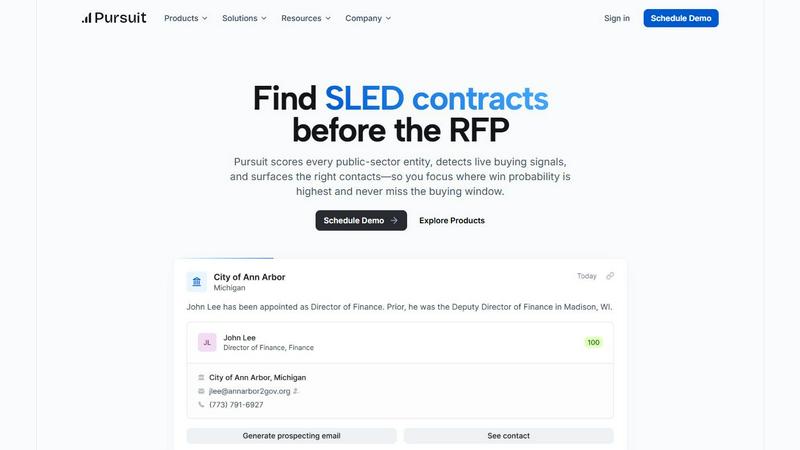
Pursuit
Pursuit uses AI to find and win public sector contracts before the RFP stage.
Last updated: February 28, 2026
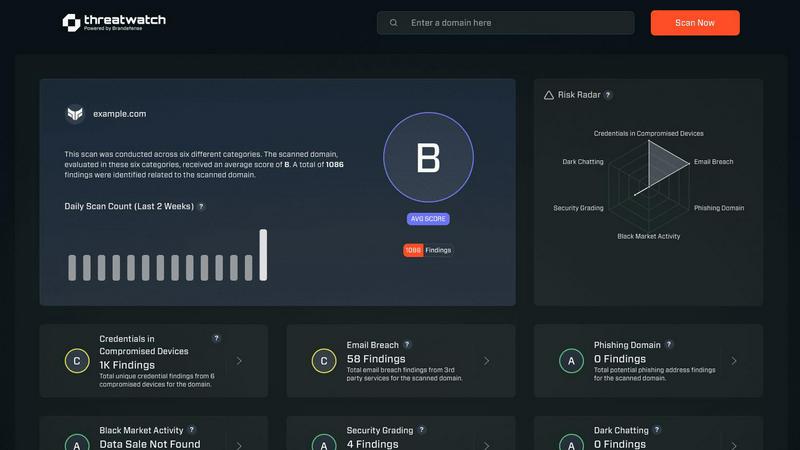
Threat Watch
Assess your cybersecurity health instantly and gain insights to strengthen defenses against emerging threats.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Pre-RFP Signal Detection
Pursuit's core AI engine scans millions of data points, including budget documents, meeting transcripts, and procurement portals, to identify genuine buying intent long before a formal solicitation appears. This feature uncovers signals like budget approvals, strategic initiatives, and contract expirations, giving your team a 6-18 month head start to build relationships and position your solution as the de facto choice before competitors are even aware.
Entity Scoring & Prioritization
The platform automatically scores and ranks every SLED entity based on a sophisticated analysis of win probability, budget alignment, and historical procurement behavior. This allows sales leaders and reps to move beyond gut feelings and focus their efforts with data-driven confidence on the accounts most likely to convert, ensuring resources are allocated to the highest-value opportunities.
Dynamic Contact & Org Chart Intelligence
Pursuit maintains a continuously enriched database of over 4 million public-sector contacts, complete with verified roles, responsibilities, and reporting structures. It goes beyond static lists by providing dynamic org charts and identifying the specific members of a buying committee for any given project, ensuring outreach is always targeted to the right person with the right context.
Native CRM & Workflow Integrations
Designed for seamless operation, Pursuit features bi-directional sync with major CRMs like Salesforce and HubSpot. Enriched account data, buying signals, and contact insights flow automatically into your existing sales stack, eliminating manual data entry and ensuring every team—from marketing to customer success—operates from the same, real-time intelligence.
Threat Watch
Real-Time Insights
Threat Watch offers real-time insights into your organization's cybersecurity landscape, allowing for immediate detection of vulnerabilities and threats. This feature ensures that users are always aware of their security posture and can act quickly to address issues as they arise.
Automated Assessments
With automated assessments, Threat Watch streamlines the process of evaluating security risks. Organizations can benefit from comprehensive evaluations without the need for extensive manual reviews, saving time and resources while enhancing security measures.
Dark Web Monitoring
One of the standout features of Threat Watch is its dark web monitoring capability. This feature scans the dark web for compromised credentials and sensitive information, providing users with critical alerts that enable them to take swift action to protect their digital identity.
Comprehensive Security Evaluations
Threat Watch evaluates multiple critical security categories, including compromised devices, breached accounts, and phishing addresses. This comprehensive approach ensures that organizations have a complete understanding of their security vulnerabilities and can prioritize their mitigation efforts effectively.
Use Cases
Pursuit
For Sales Leaders: Territory Planning & Forecasting
Sales executives use Pursuit to gain a macro view of their entire territory's potential. By analyzing entity scores and aggregated buying signals, they can identify coverage gaps, allocate resources strategically, and forecast pipeline growth based on tangible, early-stage indicators rather than lagging RFP data, leading to more predictable revenue.
For Account Executives: Strategic Deal Acceleration
AEs leverage Pursuit to become instant experts on every account. Using the Chrome extension, they can access full account intelligence, competitor insights, and recent buying signals immediately before a call. This allows them to engage as a consultative partner, reference specific budget items or initiatives, and dramatically improve win rates by demonstrating deep relevance.
For BDRs: Prioritized, High-Intent Outreach
Business Development Representatives stop cold calling blindly. Pursuit provides daily, prioritized call and outreach lists based on live signals in their territory, such as a recent budget approval for a relevant technology or a key leadership change. This transforms outreach from a numbers game into a targeted conversation, significantly increasing connection and qualification rates.
For Customer Success: Proactive Renewal & Expansion
Customer Success teams configure alerts for key renewal signals 90-180 days before a contract expires. They also monitor accounts for churn risks like budget cuts or competitor interest. This proactive intelligence allows them to initiate renewal conversations early, address concerns, and identify expansion opportunities, protecting and growing existing revenue.
Threat Watch
Small Business Cybersecurity
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch enables these organizations to quickly identify vulnerabilities, ensuring they can protect their assets without requiring a large security team.
Enterprise Risk Management
Large enterprises face complex cybersecurity challenges. Threat Watch provides a centralized solution for identifying and managing risks across diverse departments, making it easier to implement comprehensive security strategies.
Incident Response Preparation
Organizations can use Threat Watch for proactive incident response preparation. By regularly assessing their cybersecurity health, companies can develop and refine their incident response plans, ensuring they are ready to act swiftly in the event of a breach.
Compliance and Regulatory Needs
Many industries have strict compliance requirements regarding data security. Threat Watch helps organizations meet these regulations by providing detailed assessments and reports that demonstrate their commitment to cybersecurity best practices.
Overview
About Pursuit
Pursuit is the definitive AI-powered intelligence platform for businesses selling to the public sector. It is engineered to transform the historically challenging and opaque process of securing state, local, and education (SLED) contracts. The platform directly addresses the core frustrations of public-sector sales: a fragmented landscape of over 110,000 entities, hidden buying signals buried in documents, and long budget cycles where timing is everything. Pursuit's mission is to evolve sales teams from reactive RFP chasers to proactive, strategic partners. It achieves this by providing a single source of truth that scores public-sector entities to pinpoint the highest probability opportunities, uses advanced AI to detect live buying signals 6-18 months before an RFP is published, and surfaces the exact contacts needed to build a complete buying committee. With enterprise-level data on thousands of entities and millions of contacts, Pursuit empowers government contractors and technology providers to scale their revenue with precision, turning the massive scale of the SLED market from a barrier into a predictable growth engine.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution that empowers organizations to confront and conquer the ever-evolving landscape of cyber threats. By meticulously assessing assets, vulnerabilities, and exposures, Threat Watch delivers a holistic view of an organization's cybersecurity health. This tool is designed for a diverse range of businesses, from nimble startups to expansive enterprises, enabling them to swiftly identify critical security gaps. The primary value proposition of Threat Watch lies in its capability to provide real-time insights and automated assessments, equipping users with the tools to identify, prioritize, and mitigate risks effectively. As cyber threats become increasingly sophisticated, Threat Watch evolves alongside them, ensuring users are always equipped to protect their digital assets and sensitive information. With Threat Watch, organizations not only bolster their security posture but also cultivate a proactive culture of risk management, fostering resilience in the face of potential cyber adversities.
Frequently Asked Questions
Pursuit FAQ
What types of buying signals does Pursuit detect?
Pursuit's AI detects a wide range of early-stage buying indicators. These include explicit mentions of projects or needs in budget documents and council meeting minutes, contract expiration dates, leadership changes that signal new priorities, the approval of new funding or grants, and the publication of preliminary RFI or RFQ documents long before a final RFP is released.
How does Pursuit ensure data accuracy and freshness?
The platform is built on a foundation of continuous data enrichment and verification. Pursuit aggregates data from thousands of primary public sources and uses AI and human validation processes to maintain a claimed 94% accuracy rate. The system constantly monitors for updates, ensuring that contact details, org charts, and entity information are current and reliable.
Can Pursuit integrate with our existing tech stack (CRM, marketing automation)?
Yes, native integration is a key feature. Pursuit offers bi-directional sync with major CRM platforms like Salesforce and HubSpot, ensuring enriched data flows directly into your core systems. It also integrates with marketing automation tools like Marketo and advertising platforms like LinkedIn for seamless audience syncing, requiring no custom engineering work.
Is Pursuit only for large enterprises selling to the SLED market?
While extremely powerful for large government contractors, Pursuit is designed to benefit any organization targeting the SLED space, from growth-stage tech companies to established providers. The platform helps level the playing field by providing enterprise-grade intelligence, allowing smaller teams to compete effectively by focusing their efforts with the same precision as larger competitors.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes, from startups to large enterprises. Its adaptable features make it suitable for any business looking to enhance its cybersecurity measures.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms to scan the dark web for compromised credentials and sensitive information related to your organization. This proactive monitoring allows users to receive timely alerts about potential threats.
Is Threat Watch easy to integrate with existing systems?
Yes, Threat Watch is designed with ease of integration in mind. It can seamlessly connect with existing security infrastructure, enabling organizations to enhance their cybersecurity posture without disrupting their current operations.
Can Threat Watch help with compliance reporting?
Absolutely. Threat Watch provides detailed assessments and reports that can assist organizations in meeting compliance requirements related to cybersecurity, helping them demonstrate their commitment to data protection and risk management.
Alternatives
Pursuit Alternatives
Pursuit is an AI-powered business intelligence platform designed to help companies proactively win public sector contracts. It transforms the sales process by identifying buying signals long before a formal RFP is issued, allowing teams to engage as strategic partners rather than reactive bidders. Users may explore alternatives for various reasons, such as budget constraints, a need for different feature sets, or a preference for a platform that integrates with a specific tech stack. The public sector sales landscape is complex, and the right tool must align with a company's specific growth stage and operational model. When evaluating alternatives, consider platforms that offer not just data, but actionable intelligence. Look for solutions that provide deep entity insights, accurate contact information, and most importantly, the ability to detect genuine buying intent early in the procurement cycle to build a sustainable pipeline.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution that empowers organizations to assess their cybersecurity health and take actionable steps against emerging threats. Belonging to the business intelligence category, it meticulously analyzes assets, vulnerabilities, and exposures to provide a comprehensive overview of an organization’s cyber landscape. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms. When selecting an alternative, it is crucial to consider factors such as real-time threat intelligence, automated assessments, and the ability to monitor dark web activity. Ensuring that the solution aligns with your organization’s unique cybersecurity needs will facilitate a more effective defense strategy.
