Karolium vs Threat Watch
Side-by-side comparison to help you choose the right tool.
Karolium's zero-code platform accelerates digital transformation with customizable AI solutions.
Last updated: February 28, 2026
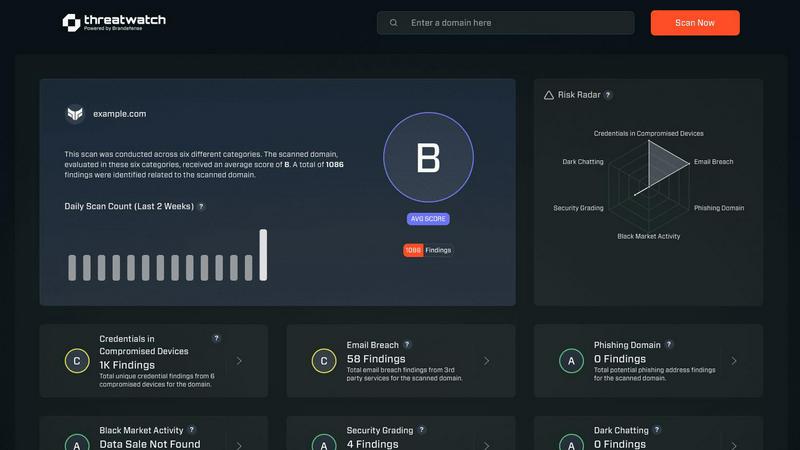
Threat Watch
Assess your cybersecurity health instantly and gain insights to strengthen defenses against emerging threats.
Last updated: March 1, 2026
Visual Comparison
Karolium

Threat Watch
Feature Comparison
Karolium
Unified Zero-Code Platform
Karolium integrates multiple platform-as-a-service capabilities—including integration, application, operations, and AI—into one unified environment. This eliminates the need for disparate tools and complex coding, providing a single canvas where business users can visually compose, customize, and deploy fully functional enterprise applications. This feature accelerates development cycles and democratizes application creation beyond IT departments.
Pre-Composed Value Chain Modules
The platform offers a suite of ready-to-use modules targeting critical business functions like Supplier Collaboration, AI-Infused Demand Forecasting, and Unified Master Data Management. These are not rigid applications but flexible, composable building blocks. Organizations can rapidly augment their existing ecosystem by deploying these modules as-is or tailoring them to specific workflows without any redevelopment from scratch.
Built-In Predictive & Prescriptive Analytics
Karolium is infused with enterprise intelligence, moving beyond simple data reporting. It features built-in AI capabilities for predictive analytics (forecasting future trends) and prescriptive analytics (recommending optimal actions). This allows users to create AI-driven applications that proactively suggest decisions, optimize operations, and transform raw data into strategic business insights.
Seamless Ecosystem Integration
Acknowledging that enterprises operate in hybrid technology landscapes, Karolium is designed for seamless integration. It connects effortlessly with both legacy systems and modern microservices-based applications. This ensures businesses can evolve their digital core without disruptive rip-and-replace projects, protecting existing investments while enabling new functionality and collaboration.
Threat Watch
Real-Time Insights
Threat Watch offers real-time insights into your organization's cybersecurity landscape, allowing for immediate detection of vulnerabilities and threats. This feature ensures that users are always aware of their security posture and can act quickly to address issues as they arise.
Automated Assessments
With automated assessments, Threat Watch streamlines the process of evaluating security risks. Organizations can benefit from comprehensive evaluations without the need for extensive manual reviews, saving time and resources while enhancing security measures.
Dark Web Monitoring
One of the standout features of Threat Watch is its dark web monitoring capability. This feature scans the dark web for compromised credentials and sensitive information, providing users with critical alerts that enable them to take swift action to protect their digital identity.
Comprehensive Security Evaluations
Threat Watch evaluates multiple critical security categories, including compromised devices, breached accounts, and phishing addresses. This comprehensive approach ensures that organizations have a complete understanding of their security vulnerabilities and can prioritize their mitigation efforts effectively.
Use Cases
Karolium
Accelerating Digital Transformation Initiatives
Organizations aiming to modernize their operations can use Karolium to rapidly build and deploy new applications—such as centralized procurement portals or contract manufacturing hubs—without the delays and complexity of traditional software development. This enables a faster transition to digital processes, helping businesses keep pace with market demands and internal growth goals.
Extending and Customizing Off-the-Shelf Software
When standard ERP or CRM systems lack specific functionality for unique workflows, Karolium provides the perfect solution. Teams can use its zero-code tools to build custom extensions, create tailored interfaces, or develop complementary applications that integrate seamlessly with the core software, thereby enhancing its value and fit without costly vendor upgrades.
Implementing AI-Driven Supply Chain Optimization
Businesses can leverage Karolium's pre-composed AI modules to inject intelligence into their supply chain. For instance, deploying AI-Infused Demand Forecasting and Lead Time Prediction modules allows for more accurate planning, reduced inventory costs, and improved responsiveness to market volatility, evolving the supply chain from a cost center to a strategic asset.
Unifying Disparate Data and Processes
Enterprises struggling with data silos and fragmented processes across departments can use Karolium as a unifying layer. By building a Unified Master Data Management application or creating integrated workflows that connect warehouse management with yard scheduling, businesses can achieve a single source of truth and enable real-time collaboration across all operational layers.
Threat Watch
Small Business Cybersecurity
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch enables these organizations to quickly identify vulnerabilities, ensuring they can protect their assets without requiring a large security team.
Enterprise Risk Management
Large enterprises face complex cybersecurity challenges. Threat Watch provides a centralized solution for identifying and managing risks across diverse departments, making it easier to implement comprehensive security strategies.
Incident Response Preparation
Organizations can use Threat Watch for proactive incident response preparation. By regularly assessing their cybersecurity health, companies can develop and refine their incident response plans, ensuring they are ready to act swiftly in the event of a breach.
Compliance and Regulatory Needs
Many industries have strict compliance requirements regarding data security. Threat Watch helps organizations meet these regulations by providing detailed assessments and reports that demonstrate their commitment to cybersecurity best practices.
Overview
About Karolium
Karolium represents the next evolutionary stage in enterprise software, a unified zero-code platform engineered to propel businesses from static operations to dynamic, intelligent growth. It is a holistic ecosystem that merges the power of iPaaS, aPaaS, oPaaS, and AIPaaS into a single, cohesive environment. This platform is designed for forward-thinking organizations seeking to accelerate their digital transformation, overcome the rigidity of off-the-shelf solutions, and unlock greater value from their existing technology investments. By providing a library of ready-to-deploy, pre-composed modules and a completely code-free environment for customization, Karolium empowers teams to rapidly build, extend, and tailor intelligent business applications at 10x the traditional speed. Its core value proposition lies in delivering enterprise-grade agility, enabling seamless integration with legacy and modern systems, and embedding predictive and prescriptive AI directly into business workflows. This allows companies to progress from reactive problem-solving to proactive, data-driven strategy, fostering measurable improvements in efficiency, collaboration, and strategic decision-making across the entire value chain.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution that empowers organizations to confront and conquer the ever-evolving landscape of cyber threats. By meticulously assessing assets, vulnerabilities, and exposures, Threat Watch delivers a holistic view of an organization's cybersecurity health. This tool is designed for a diverse range of businesses, from nimble startups to expansive enterprises, enabling them to swiftly identify critical security gaps. The primary value proposition of Threat Watch lies in its capability to provide real-time insights and automated assessments, equipping users with the tools to identify, prioritize, and mitigate risks effectively. As cyber threats become increasingly sophisticated, Threat Watch evolves alongside them, ensuring users are always equipped to protect their digital assets and sensitive information. With Threat Watch, organizations not only bolster their security posture but also cultivate a proactive culture of risk management, fostering resilience in the face of potential cyber adversities.
Frequently Asked Questions
Karolium FAQ
What is a zero-code platform, and who can use Karolium?
A zero-code platform allows users to create software applications through visual interfaces and configuration instead of writing traditional programming code. Karolium is designed for both business analysts and IT professionals. Business teams can compose applications to solve immediate needs, while IT can govern the platform and handle complex integrations, making advanced application development accessible across the organization.
How does Karolium handle integration with our existing systems?
Karolium is built as an integration-friendly iPaaS at its core. It comes with pre-built connectors and tools designed to facilitate seamless integration with a wide array of legacy systems, databases, cloud services, and modern APIs. This allows Karolium to act as a cohesive layer that augments your current application ecosystem without requiring disruptive replacements.
Can we truly customize applications without any coding?
Yes. Karolium's platform is founded on complete composability and a code-free environment. Its pre-composed modules are designed to be modified visually—you can alter workflows, data models, user interfaces, and business rules using drag-and-drop designers and property settings. This allows for deep customization to match your exact business processes without developer intervention.
What kind of support and updates can we expect?
Karolium is delivered as a managed PaaS-driven SaaS platform. This means you receive continuous access to the latest platform capabilities, security patches, and regular enhancements to the value-chain solution modules. The company typically releases new modules and features on a quarterly basis, ensuring your investment evolves alongside technological and market advancements.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes, from startups to large enterprises. Its adaptable features make it suitable for any business looking to enhance its cybersecurity measures.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms to scan the dark web for compromised credentials and sensitive information related to your organization. This proactive monitoring allows users to receive timely alerts about potential threats.
Is Threat Watch easy to integrate with existing systems?
Yes, Threat Watch is designed with ease of integration in mind. It can seamlessly connect with existing security infrastructure, enabling organizations to enhance their cybersecurity posture without disrupting their current operations.
Can Threat Watch help with compliance reporting?
Absolutely. Threat Watch provides detailed assessments and reports that can assist organizations in meeting compliance requirements related to cybersecurity, helping them demonstrate their commitment to data protection and risk management.
Alternatives
Karolium Alternatives
Karolium is a zero-code development platform designed to accelerate digital transformation by enabling businesses to build custom, AI-driven applications. It belongs to the category of enterprise-grade, no-code/low-code solutions that prioritize agility and deep customization without requiring traditional programming skills. Users often explore alternatives for various reasons, such as budget constraints, specific feature requirements not covered by the platform, or the need for a different balance between simplicity and technical depth. Some organizations may also seek tools that align more closely with their existing tech stack or offer a different approach to scalability and integration. When evaluating alternatives, it's crucial to consider your organization's current growth stage and future trajectory. Look for a platform that matches your technical team's capabilities, offers the right level of analytics and AI functionality, and can integrate smoothly with your core systems. The goal is to find a solution that evolves with your business, supporting both immediate operational needs and long-term strategic innovation.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution that empowers organizations to assess their cybersecurity health and take actionable steps against emerging threats. Belonging to the business intelligence category, it meticulously analyzes assets, vulnerabilities, and exposures to provide a comprehensive overview of an organization’s cyber landscape. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms. When selecting an alternative, it is crucial to consider factors such as real-time threat intelligence, automated assessments, and the ability to monitor dark web activity. Ensuring that the solution aligns with your organization’s unique cybersecurity needs will facilitate a more effective defense strategy.
