iGPT vs Threat Watch
Side-by-side comparison to help you choose the right tool.
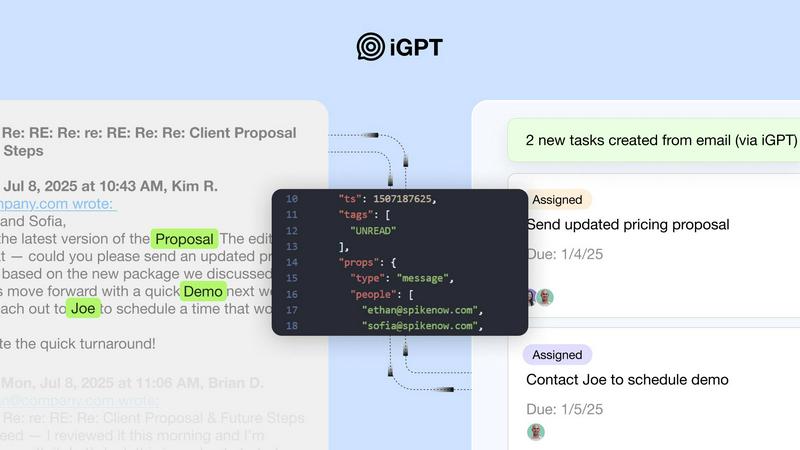
iGPT transforms email data into actionable insights, streamlining enterprise workflows with a secure, context-aware API.
Last updated: March 1, 2026
Threat Watch
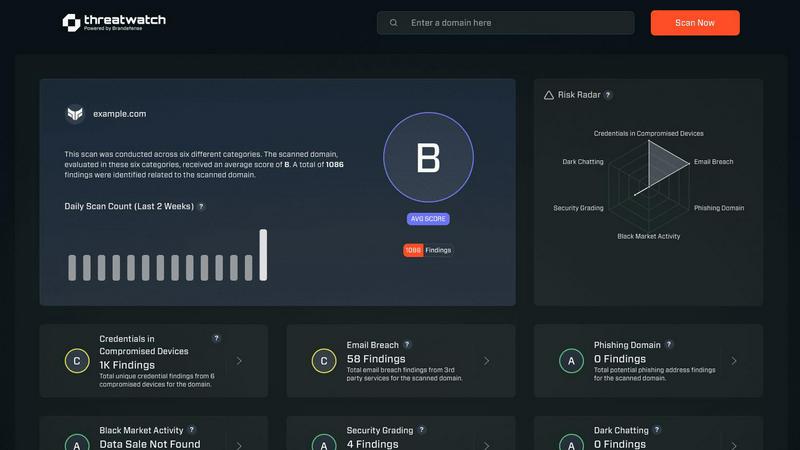
Assess your cybersecurity health instantly and gain insights to strengthen defenses against emerging threats.
Last updated: March 1, 2026
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Immediate Integration
iGPT offers an SDK and a live playground for swift testing of requests and responses, allowing businesses to seamlessly integrate the API with their existing systems. This feature ensures that users can start leveraging email intelligence quickly and efficiently without lengthy onboarding processes.
Contextual Responses
The API delivers responses that are not only ready for reasoning and automation but also include citations back to the source. This means that every answer provided by iGPT is anchored in a verifiable context, making it easier for organizations to trace back information and maintain accuracy.
Real-time Ingestion
iGPT excels in real-time data processing. It indexes new messages and attachments instantly, ensuring that the information is always up-to-date. This feature helps businesses keep track of ongoing conversations and changes, enhancing their ability to respond promptly.
Compliance and Audit Trail
With a focus on security, iGPT provides a full audit trail for every interaction. Organizations can trace feedback, approvals, and rationales back to original conversations, ensuring accountability and transparency in their email communications.
Threat Watch
Real-Time Insights
Threat Watch offers real-time insights into your organization's cybersecurity landscape, allowing for immediate detection of vulnerabilities and threats. This feature ensures that users are always aware of their security posture and can act quickly to address issues as they arise.
Automated Assessments
With automated assessments, Threat Watch streamlines the process of evaluating security risks. Organizations can benefit from comprehensive evaluations without the need for extensive manual reviews, saving time and resources while enhancing security measures.
Dark Web Monitoring
One of the standout features of Threat Watch is its dark web monitoring capability. This feature scans the dark web for compromised credentials and sensitive information, providing users with critical alerts that enable them to take swift action to protect their digital identity.
Comprehensive Security Evaluations
Threat Watch evaluates multiple critical security categories, including compromised devices, breached accounts, and phishing addresses. This comprehensive approach ensures that organizations have a complete understanding of their security vulnerabilities and can prioritize their mitigation efforts effectively.
Use Cases
iGPT
Email Assistants
Organizations can build intelligent email agents that efficiently draft, prioritize, and act on emails with complete context. This capability allows teams to save time and reduce the cognitive load associated with managing email tasks.
Workflow Automation
iGPT enables businesses to convert email threads into actionable tasks, deadlines, and approvals. By flagging items that are stuck, organizations can streamline their workflow processes and ensure that nothing falls through the cracks.
Customer Support Copilots
With iGPT, businesses can reconstruct full customer stories across lengthy email threads, including attachments and tone shifts. This functionality helps support teams provide personalized, informed responses to customer inquiries.
Insights from Attachments
The API allows for summarizing information from various file types, such as invoices, contracts, and spreadsheets, within the context of the associated email thread. This feature enhances the decision-making process by providing relevant insights directly tied to communication history.
Threat Watch
Small Business Cybersecurity
Small businesses often lack the resources for extensive cybersecurity measures. Threat Watch enables these organizations to quickly identify vulnerabilities, ensuring they can protect their assets without requiring a large security team.
Enterprise Risk Management
Large enterprises face complex cybersecurity challenges. Threat Watch provides a centralized solution for identifying and managing risks across diverse departments, making it easier to implement comprehensive security strategies.
Incident Response Preparation
Organizations can use Threat Watch for proactive incident response preparation. By regularly assessing their cybersecurity health, companies can develop and refine their incident response plans, ensuring they are ready to act swiftly in the event of a breach.
Compliance and Regulatory Needs
Many industries have strict compliance requirements regarding data security. Threat Watch helps organizations meet these regulations by providing detailed assessments and reports that demonstrate their commitment to cybersecurity best practices.
Overview
About iGPT
iGPT is an innovative email intelligence API designed to revolutionize how enterprises manage their email communications. By transforming both email messages and attachments into actionable insights, it empowers organizations to make informed decisions, streamline task management, and enhance operational efficiency. Targeted at businesses seeking to optimize their workflows, iGPT offers a robust enterprise-grade infrastructure that ensures secure and auditable access to communication data. The API provides context-aware responses that facilitate quick decision-making, eliminating the complexities associated with traditional email parsing. With real-time indexing and seamless integration into existing systems, iGPT allows enterprises to deploy AI-driven agents that can confidently interpret and utilize email data while ensuring compliance and maintaining trust. By harnessing the full potential of email communications, iGPT is at the forefront of a transformative shift in enterprise productivity.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution that empowers organizations to confront and conquer the ever-evolving landscape of cyber threats. By meticulously assessing assets, vulnerabilities, and exposures, Threat Watch delivers a holistic view of an organization's cybersecurity health. This tool is designed for a diverse range of businesses, from nimble startups to expansive enterprises, enabling them to swiftly identify critical security gaps. The primary value proposition of Threat Watch lies in its capability to provide real-time insights and automated assessments, equipping users with the tools to identify, prioritize, and mitigate risks effectively. As cyber threats become increasingly sophisticated, Threat Watch evolves alongside them, ensuring users are always equipped to protect their digital assets and sensitive information. With Threat Watch, organizations not only bolster their security posture but also cultivate a proactive culture of risk management, fostering resilience in the face of potential cyber adversities.
Frequently Asked Questions
iGPT FAQ
What types of organizations can benefit from iGPT?
iGPT is designed for enterprises of all sizes looking to optimize their email workflows and enhance communication efficiency. It is particularly beneficial for businesses that rely heavily on email for operational processes.
How does iGPT ensure data security?
iGPT implements enterprise-grade security measures, including zero data retention and role-based access control (RBAC). This ensures that all data processed through the API remains confidential and secure, protecting it from unauthorized access.
Can iGPT integrate with existing systems?
Yes, iGPT features immediate integration capabilities through its SDK and unified endpoint, allowing organizations to connect email sources seamlessly and utilize email intelligence without disruption.
What makes iGPT different from traditional email parsing solutions?
Unlike traditional solutions that require extensive parsing and prompt tuning, iGPT simplifies the process by providing a single unified endpoint for retrieval, context shaping, and reasoning, thereby enhancing efficiency and reducing complexity.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for organizations of all sizes, from startups to large enterprises. Its adaptable features make it suitable for any business looking to enhance its cybersecurity measures.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms to scan the dark web for compromised credentials and sensitive information related to your organization. This proactive monitoring allows users to receive timely alerts about potential threats.
Is Threat Watch easy to integrate with existing systems?
Yes, Threat Watch is designed with ease of integration in mind. It can seamlessly connect with existing security infrastructure, enabling organizations to enhance their cybersecurity posture without disrupting their current operations.
Can Threat Watch help with compliance reporting?
Absolutely. Threat Watch provides detailed assessments and reports that can assist organizations in meeting compliance requirements related to cybersecurity, helping them demonstrate their commitment to data protection and risk management.
Alternatives
iGPT Alternatives
iGPT is an advanced email intelligence API that helps enterprises convert their email communications and attachments into actionable insights. Positioned within the business intelligence category, iGPT offers organizations a secure and efficient way to enhance operational workflows through context-aware responses and real-time data processing. Users often seek alternatives to iGPT due to a variety of reasons, including pricing, specific feature sets, or compatibility with existing platforms. When exploring alternatives, it’s essential to consider factors such as ease of integration, scalability, data security, and the ability to meet unique business requirements. A thorough evaluation will ensure that the chosen solution aligns with the organization's growth objectives and operational needs.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution that empowers organizations to assess their cybersecurity health and take actionable steps against emerging threats. Belonging to the business intelligence category, it meticulously analyzes assets, vulnerabilities, and exposures to provide a comprehensive overview of an organization’s cyber landscape. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms. When selecting an alternative, it is crucial to consider factors such as real-time threat intelligence, automated assessments, and the ability to monitor dark web activity. Ensuring that the solution aligns with your organization’s unique cybersecurity needs will facilitate a more effective defense strategy.
