Alternatives to Threat Watch
Assess your cybersecurity health instantly and gain insights to strengthen defenses against emerging threats.
Explore 16 alternatives to Threat Watch. Compare features, pricing, and find the best fit for your needs.
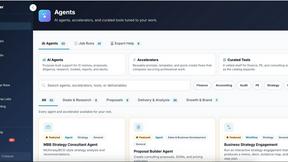
Decker
Decker evolves your consulting work from prompts to polished deliverables with AI workflows, expert support, and a monetization engine for your.

FX Radar
FX Radar evolves your trading with real-time news and AI-driven logic, delivering market-moving headlines in seconds for smarter decisions.

AI Business Name Generator
Unlock your brand's potential with our AI Business Name Generator, crafting unique and memorable names for your startup or company in seconds.
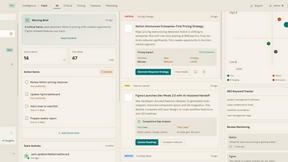
ROIpad
ROIpad delivers data-driven insights to refine your B2B SaaS positioning, helping you target the right segments and accelerate growth.

Opal44
Opal44 simplifies your website analytics with AI-driven insights in plain English for smarter, data-informed decisions.

Fusedash
Fusedash transforms raw data into intuitive dashboards and charts, empowering teams to make informed decisions swiftly.
finban
finban empowers confident liquidity planning, helping you manage hiring, taxes, and investments without Excel chaos.

aVenture
aVenture evolves startup research with AI to map companies and track funding opportunities.

iGPT
iGPT transforms email data into actionable insights, streamlining enterprise workflows with a secure, context-aware API.

Karolium
Karolium's zero-code platform accelerates digital transformation with customizable AI solutions.
Promotron
Promotron accelerates promotional sales with cloud software that automates e-commerce and custom printing for industry.
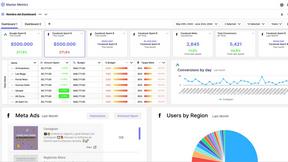
Master Metrics
Master Metrics evolves your data into clear dashboards and smart alerts for confident growth.

CMMC ROI
CMMC ROI calculates your compliance costs and investment returns to secure DoD contracts.
Deeploy
Deeploy empowers organizations to govern and scale AI confidently, ensuring compliance and minimizing risks effectively.
About Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution that empowers organizations to assess their cybersecurity health and take actionable steps against emerging threats. Belonging to the business intelligence category, it meticulously analyzes assets, vulnerabilities, and exposures to provide a comprehensive overview of an organization’s cyber landscape. Users often seek alternatives to Threat Watch for various reasons, including pricing, specific feature sets, or compatibility with their existing platforms. When selecting an alternative, it is crucial to consider factors such as real-time threat intelligence, automated assessments, and the ability to monitor dark web activity. Ensuring that the solution aligns with your organization’s unique cybersecurity needs will facilitate a more effective defense strategy.
FAQs about Threat Watch Alternatives
What is Threat Watch?
Threat Watch is a cybersecurity intelligence solution designed to help organizations assess their cyber health and gain insights into mitigating risks.
Who is Threat Watch for?
Threat Watch is tailored for businesses of all sizes, from startups to large enterprises, seeking to enhance their security posture.
Is Threat Watch free?
Threat Watch is a premium solution, and pricing details can vary based on the features and services required.
What are the main features of Threat Watch?
The main features include real-time threat intelligence, automated vulnerability assessments, and dark web monitoring.